 By Dr. Darren Hayes, Director of the Seidenberg Cybersecurity Institute.
By Dr. Darren Hayes, Director of the Seidenberg Cybersecurity Institute.
James Ossipov, Investigator from the Westchester County District Attorney’s Office, returned recently to his alma mater, the Seidenberg School of CSIS, to discuss the future of mobile forensics. Appropriately, Mr. Ossipov returned on Veterans Day; James has a distinguished military career and still continues to serve today. His talk was delivered to prospective computer forensics experts taking a Mobile Forensics Investigations class with Dr. Darren Hayes.
In recent times, Apple has moved from software encryption to hardware encryption. Much to the chagrin of law enforcement, companies, like Apple, have left the keys to decrypt the latest iPhones on the device itself. This makes it virtually impossible for examiners to access the device of an uncooperative suspect. To put it into perspective, the iPhone 9, with its six-digit PIN, has 10,000,000 possible combinations. With each unsuccessful try, Apple has built in an ever-increasing time delay within which you can enter a different PIN. Investigators are experiencing similar challenges with Android devices running Lollipop and Marshmallow. The future of mobile forensics is perplexing but not bleak according to James, who finds these challenges scintillating.
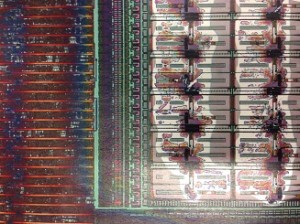 Brute forcing a PIN is sometimes possible with Field Programmable Gate Arrays (FPGA), which can be configured to crack a PIN in a fraction of the time it takes a traditional computer to do. The next solution will cost each forensics lab a minimum of $1 million to get into the game. The chip must be removed, and gases applied to remove the casing. Ultimately, an attack will be launched on the chip using an electron microscope and that is where the highest cost lies. Today, some of these high-tech experts are charging $25,000 and even up to $1 million to access smartphones with full-disk encryption. We are certainly entering some interesting times in the world of mobile forensics.
Brute forcing a PIN is sometimes possible with Field Programmable Gate Arrays (FPGA), which can be configured to crack a PIN in a fraction of the time it takes a traditional computer to do. The next solution will cost each forensics lab a minimum of $1 million to get into the game. The chip must be removed, and gases applied to remove the casing. Ultimately, an attack will be launched on the chip using an electron microscope and that is where the highest cost lies. Today, some of these high-tech experts are charging $25,000 and even up to $1 million to access smartphones with full-disk encryption. We are certainly entering some interesting times in the world of mobile forensics.

