by Andreea Cotoranu
Clinical Professor, Information Technology
A team of eight Seidenberg students with a passion for cybersecurity, participated in the highly coveted Collegiate Cyber Defense Competition, Northeast (NECCDC) qualifier, on January 23, 2021. The ‘core eight’ team included: Logan Cusano (BS in Information Technology ’22 – captain/student coach), Alexander Zimmer (MS in Cybersecurity ’22), Alexs Wijoyo (BS in Computer Science ’22), Kyle Hanson (BS in Information Systems’21), Brendan Scollan (BS in Information Technology ’24), Zachary Goldberg (BS in Information Technology ’22), Andrew Iadevaia (BS in Computer Science ’23), and Aleks Ceremisinovs (BA in Computer Science ’21).
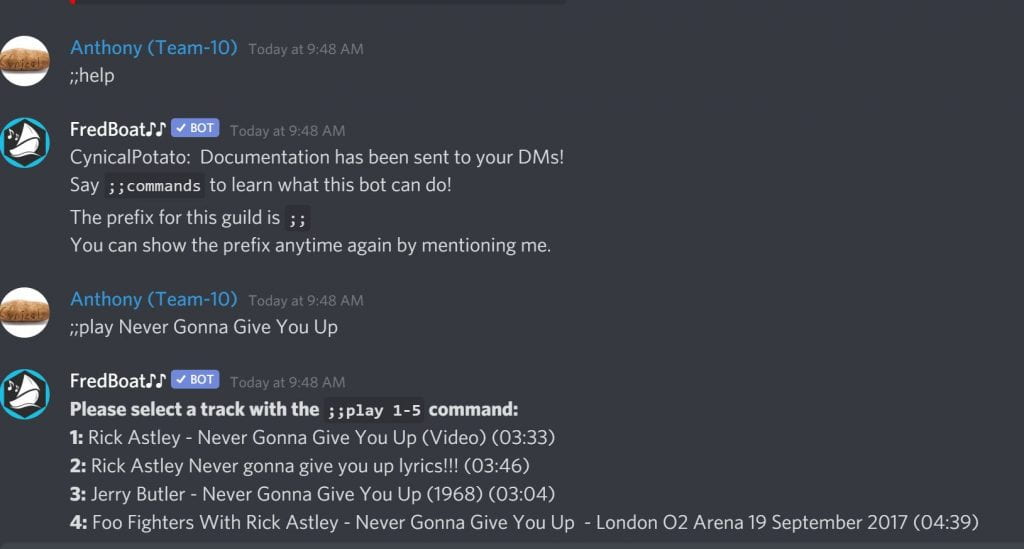
One of the competition goals is to “develop competitor skills to respond to modern cybersecurity threats.” The competition provides a controlled environment for students and challenges them to protect an enterprise network infrastructure and business information system against inherent challenges. The competition environment, called ‘cyber range,’ was virtual, and the communication and collaboration were supported over Discord. Industry professionals moderated the teams; the ‘core eight’ were moderated by Seidenberg alums, and former NECCDC competitors, Andrew Ku (NYC Cyber Command) and John Guckian (IBM).
The theme of this year’s competition was ‘mobility.’ In the qualifier scenario, the ‘core eight’ were part of a news organizations’ internal security team working to administer and secure both data and systems of a regional office in the face of challenges posed by COVID-19. Competing teams were expected to manage the network, keep it operational, prevent unauthorized access, maintain and provide public and internal services.
As part of the competition, a ‘red team’ played the attacker role aiming to compromise the team’s systems. The ‘red team’ launched attacks by making extensive use of bots. Memes and a curated playlist contributed to creating a suspenseful competition atmosphere, which accurately reflected the realities of the battle between the ‘red team’ and the competing teams.
As the team captain for the event, Logan Cusano ’22 explained that his role was to assign tasks and secure servers. He noted that his favorite part of his role was seeing new team members “learn an immense amount of information and real-world skills on their assigned operating systems.”
Another team member, Alex Zimmer ’22, explained that he “assisted in our team’s logistical planning as well the preparation of script and reference materials. I also played an active role with our log management on the day of the competition. I found it particularly satisfying when either my materials or advice allowed another team member to overcome an obstacle or properly counter red team actions.”
Alexs Wijoyo ’22, who specialized in Linux operating systems on the team, explained that “the best part of my task was that I was able to get my hand dirty with the tools and operation of the competition. I love these types of things.”
To start, the team had to tame bots with correct command lines to obtain clues and access resources. After that, it was up to keeping systems secure and services up against several rounds of attacks, over five hours. By round 7, the team had 26/28 services up and running, by round 20 it was down to 11/28, and by round 27, the team rebounded to 17/28. However, by round 41, it was down to 9/28, then up to 15/28 by round 52 – they were never gonna give those services up! Business tasks, called injects, were as important as keeping services up, especially when competing against great teams. Ultimately, the performance on both technical and business tasks contributed to the team’s qualification to the NECCDC regionals.

Alex, who recalled the experience of “the continuous monitoring of the possible attack angles” as a combination of exhilarating and strenuous, explained that the team was ecstatic when they learned of their qualification.
“When I read the news that we had made it to the next round I was elated. I knew the team was capable but this just proved me right,” Logan said of the team’s excitement.
“We love working together and we sure do get a thrill from it,” Alexs chimed in.
Overall, the competition was challenging; however, ‘the core eight’ succeeded to communicate and collaborate, in a virtual environment, under pressure – any IT team would be lucky to have them on board. (Note: for a red team review of last year’s competition and advice for competitors, check Tom Kopchak’s (Hurricane Labs) post.
Seventeen teams from the Northeast region participated in this competition. Ten qualifying teams, including Pace, will now have the opportunity to participate in the 2021 Northeast Regional CCDC, taking place virtually, March 19-21, through the Cyber Range and Training Center, part of the Global Cybersecurity Institute (GCI) within Rochester Institute of Technology (RIT) – the host organization for 2021.
As reported by current and former participants, competitions like NECCDC are some of the most impactful learning experiences. Pace students interested in participating in cybersecurity competitions are encouraged to connect with BergCyberSec, the Pace Cybersecurity Club (Discord: BergCyberSec) to learn of opportunities for training and collaboration.
Are you interested in pursuing a course, a degree, or a career in the exciting domain of cybersecurity? Check the Seidenberg School at Pace University’s cybersecurity course and program offerings here.
Pace University recently launched a Master of Science in Cybersecurity that aims to train the next generation of cybersecurity professionals to join an ever-growing workforce.